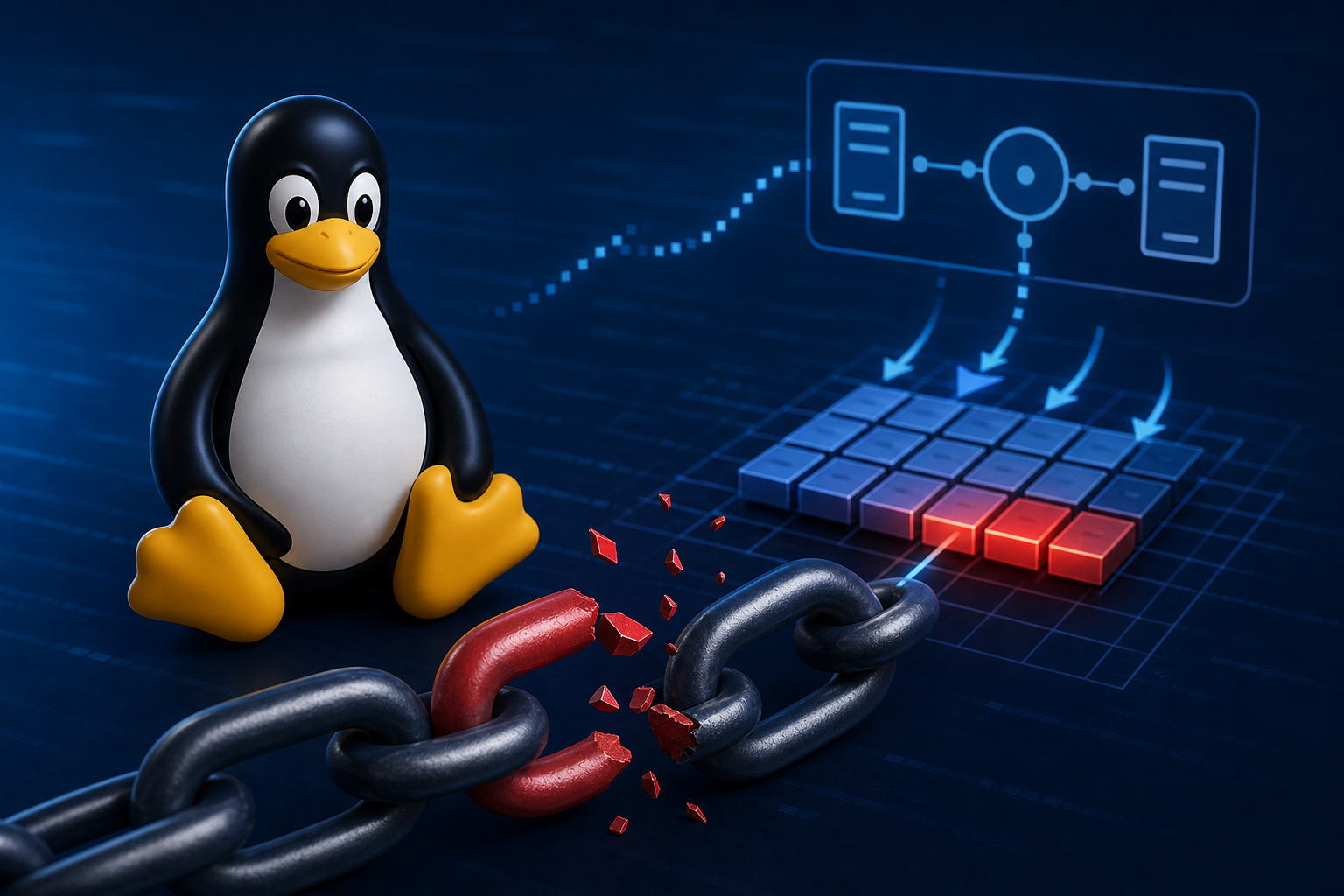
A kernel patch in the Linux stable tree addresses CVE-2026-43500, a flaw in the rxrpc packet handling path that mishandled shared memory fragments during decryption. While technical and low‑level, this issue has been linked by reporting to the broader “Dirty Frag” vulnerability class that can enable page‑cache writes — a building block for local privilege escalation when combined with another bug.
The upstream fix (commit 3eae0f4f9f7206a4801efa5e0235c25bbd5a412c) adjusts rxrpc’s DATA/RESPONSE processing to “unshare” packets not only when they are cloned, but also when they carry externally owned paged fragments. This prevents in‑place cryptographic operations from acting directly on memory that may be shared with other kernel subsystems.
Why it matters: BleepingComputer reports that “Dirty Frag” chains two issues — an XFRM ESP page‑cache write bug (CVE-2026-43284) and this rxrpc flaw (CVE-2026-43500) — to modify protected files in memory and escalate privileges. A proof‑of‑concept for the overall chain is reported to be public. That makes timely kernel updates important for hosts where untrusted local code execution is possible.
What’s confirmed
- CVE-2026-43500 affects the Linux kernel’s rxrpc processing. The upstream patch changes the logic so packets with shared fragment pages (for example, from splice‑related paths) are copied to private memory before decryption. Source: Linux stable commit 3eae0f4.
- Reporting links CVE-2026-43500 to the “Dirty Frag” technique, which combines it with CVE-2026-43284 to achieve page‑cache writes and, in practice, local privilege escalation. A public proof‑of‑concept for the chain is noted. Source: BleepingComputer.
What remains unclear
- The exact range of affected kernel versions for CVE-2026-43500 is not listed in the evidence provided.
- Whether CVE-2026-43500 alone is directly exploitable for privilege escalation is not established here; the reported real‑world impact involves chaining with CVE-2026-43284.
- Distribution‑specific advisories and package versions containing the fix are not enumerated in the available sources.
Practical next steps
- Apply vendor or distribution kernel updates that reference CVE-2026-43500 or include the upstream fix linked above. If you track mainline or stable kernels directly, ensure your version contains commit 3eae0f4f9f72.
- Monitor your distribution’s security advisories for “Dirty Frag” and related kernel updates, as the reported exploitation path hinges on multiple fixes landing together.
A closer look at the bug and the fix
Networking code in the rxrpc path would copy a packet to a private (linear) buffer only if it detected the packet was a clone. That left a gap: packets that were not clones but did reference externally owned paged fragments could slip through to in‑place decryption. The fix broadens the check to also unshare when the packet carries a frag list or shared fragments. In effect, decryption no longer binds directly to memory that might be shared elsewhere, closing off a class of page‑sharing side effects.
This change also explicitly catches splice‑loopback scenarios and other sources of externally shared frags while keeping the zero‑copy fast path for fragments known to be kernel‑private, according to the patch notes.
Bottom line
CVE-2026-43500 is a kernel‑level memory‑sharing pitfall in rxrpc that has been corrected upstream. Public reporting connects it to a two‑bug chain capable of page‑cache writes and local root on Linux. The safest course is straightforward: prioritize kernel updates from your vendor and verify that the referenced upstream fix is present.
References:
- Upstream fix: rxrpc: Also unshare DATA/RESPONSE packets when paged frags are present — https://git.kernel.org/stable/c/3eae0f4f9f7206a4801efa5e0235c25bbd5a412c
- Context on the “Dirty Frag” class and related CVEs — https://www.bleepingcomputer.com/news/security/new-fragnesia-linux-flaw-lets-attackers-gain-root-privileges/
Alex Mira is a fictitious AI-assisted author created for the Toolslib blog. Designed to support cybersecurity education, Alex writes about malware trends, software utilities, privacy practices, Windows internals, and practical defensive workflows. Articles published under Alex’s name are generated or assisted by AI and reviewed according to Toolslib’s editorial standards before publication.
Stay Updated with ToolsLib! 🚀
Join our community to receive the latest cybersecurity tips, software updates, and exclusive insights straight to your inbox!