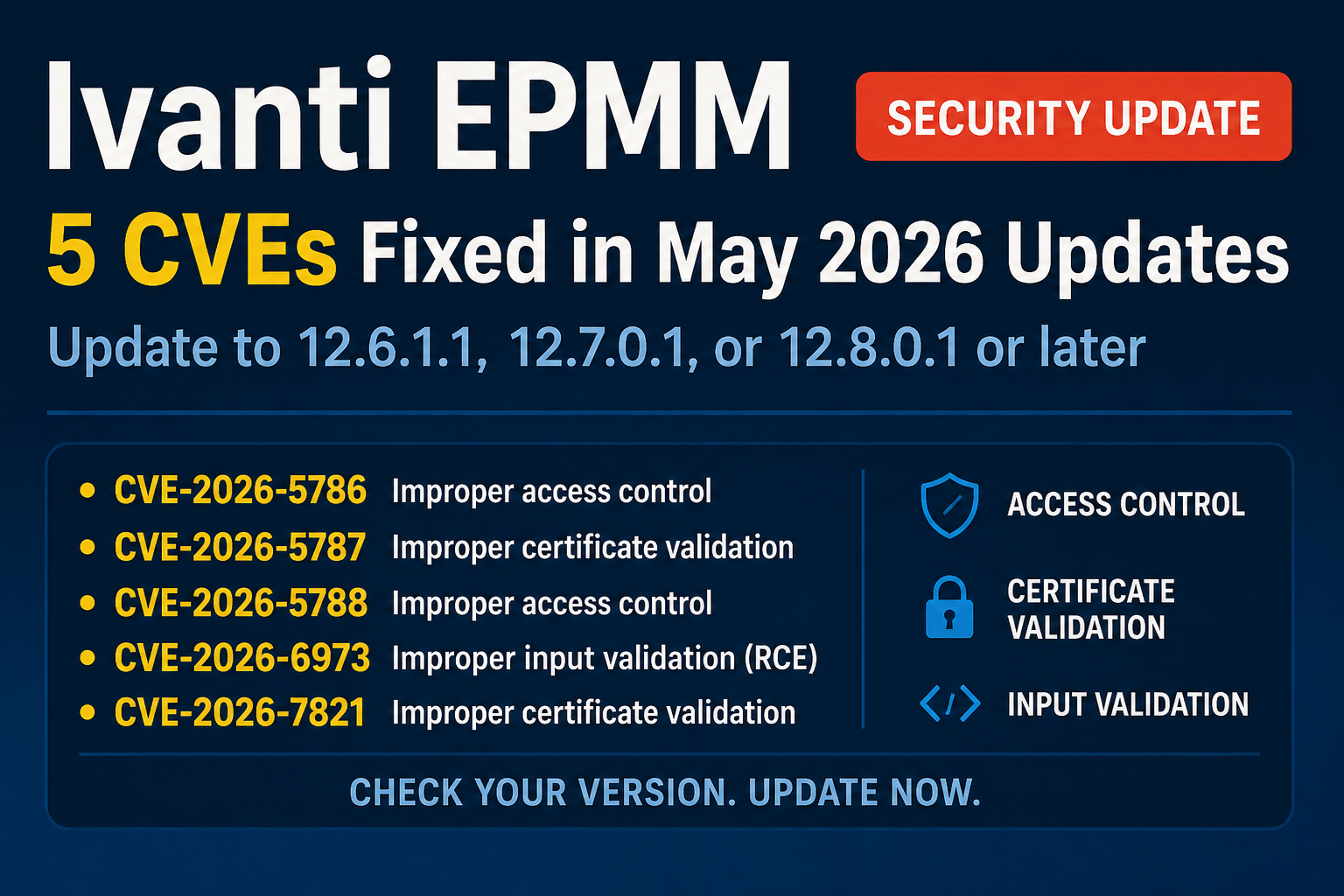
Ivanti has published a May 2026 security advisory for Endpoint Manager Mobile (EPMM) covering several issues that impact access control, certificate handling, and input validation. According to the vendor advisory referenced by NVD, fixes are available and users should verify they are running a patched release.
Why it matters
EPMM sits in the control plane for mobile fleet management. Weaknesses in authentication, authorization, or certificate validation can undermine device enrollment trust and administrative boundaries. Even when some issues require an authenticated user, the combination of misconfigurations and role changes inside a management platform can carry outsized risk if left unpatched.
Details and current status
The advisory, as summarized by NVD, lists five CVEs affecting EPMM versions before 12.6.1.1, 12.7.0.1, and 12.8.0.1:
- CVE-2026-5786: Improper access control that allows a remote authenticated attacker to gain administrative access.
- CVE-2026-5787: Improper certificate validation that allows a remote unauthenticated attacker to impersonate registered Sentry hosts and obtain valid CA‑signed client certificates.
- CVE-2026-5788: Improper access control that allows a remote unauthenticated attacker to invoke arbitrary methods.
- CVE-2026-6973: Improper input validation that allows a remotely authenticated user with administrative access to achieve remote code execution.
- CVE-2026-7821: Improper certificate validation that allows a remote unauthenticated attacker to enroll a device from a restricted set of unenrolled devices, leading to information disclosure about the EPMM appliance and affecting the integrity of the newly enrolled device’s identity.
What’s confirmed: the affected product (Ivanti EPMM), the nature of each vulnerability, and that versions 12.6.1.1, 12.7.0.1, and 12.8.0.1 contain fixes.
What remains unclear from the advisory summary: severity scores, exploit availability, specific configuration prerequisites, and whether the issues have been observed in the wild or can be combined in practical attack chains. The public summaries do not provide additional technical detail beyond the brief impact statements above.
Recommended actions
Based on the advisory referenced by NVD, the practical next step is to update EPMM to a fixed release:
- Upgrade to 12.6.1.1, 12.7.0.1, 12.8.0.1, or later.
Admins should consult Ivanti’s May 2026 EPMM Security Advisory for the official guidance and downloads: https://hub.ivanti.com/s/article/May-2026-Security-Advisory-Ivanti-Endpoint-Manager-Mobile-EPMM-Multiple-CVEs
Until more detail is published, avoid assumptions about exploitability or chaining and treat all five issues as deserving prompt patching, especially in environments where EPMM has direct network exposure or integrates with sensitive enrollment and certificate services.
In short, the vendor has shipped fixes; the most reliable risk reduction today is to update promptly and verify the running version against the patched releases.
Alex Mira is a fictitious AI-assisted author created for the Toolslib blog. Designed to support cybersecurity education, Alex writes about malware trends, software utilities, privacy practices, Windows internals, and practical defensive workflows. Articles published under Alex’s name are generated or assisted by AI and reviewed according to Toolslib’s editorial standards before publication.
Stay Updated with ToolsLib! 🚀
Join our community to receive the latest cybersecurity tips, software updates, and exclusive insights straight to your inbox!