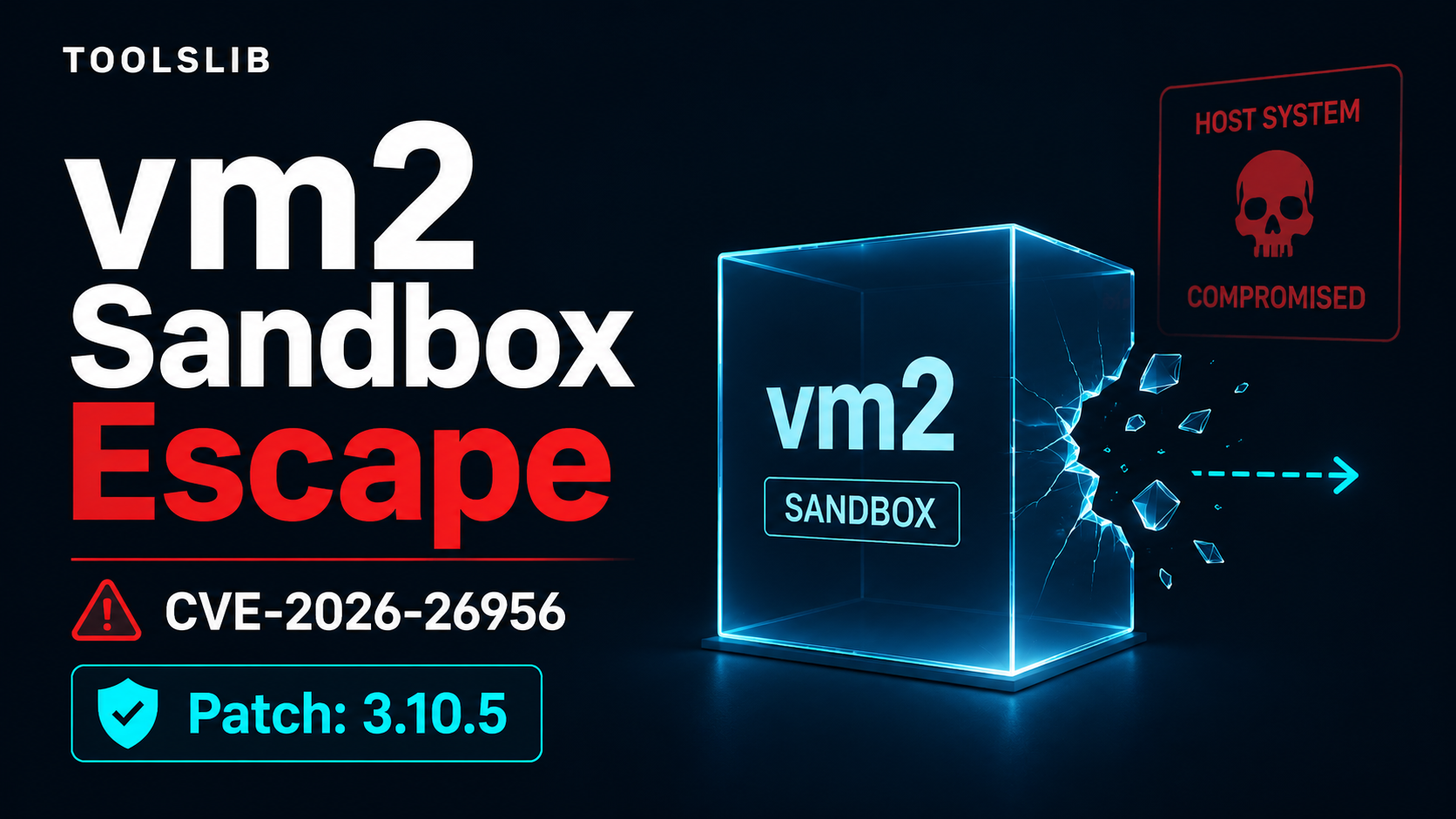
A newly disclosed vulnerability in the popular Node.js sandboxing library vm2 allows code running inside the sandbox to break out and execute on the host. Tracked as CVE-2026-26956, the issue has been confirmed to affect vm2 version 3.10.4, with a patch available in 3.10.5 according to the NVD summary. BleepingComputer reports that the maintainer’s advisory ties exploitation to Node.js 25 (confirmed on 25.6.1) when WebAssembly exception handling and JSTag support are enabled. Public proof-of-concept code has been released.
vm2 is widely used to execute untrusted JavaScript with restricted access to process and filesystem APIs. It underpins online coding platforms, automation tooling, and various SaaS workflows, with millions of weekly downloads on npm. A sandbox escape undermines the core trust boundary those services rely on.
Why it matters
When a sandbox fails, attacker-controlled code can reach the host environment. For CVE-2026-26956, NVD states that code running inside VM.run() can obtain the host process object and run commands without cooperation from the host. With a published PoC and broad adoption of vm2, environments that match the impacted configuration should treat this as a priority.
What’s confirmed versus unclear
Based on the available reports:
- Confirmed facts
- Affected version: vm2 3.10.4 is vulnerable to a full sandbox escape with arbitrary code execution (NVD).
- Fix: The issue is patched in vm2 3.10.5 (NVD). The project has release notes for 3.10.5 on GitHub.
- Impacted environments: The maintainer’s advisory, as relayed by BleepingComputer, says exploitation has been confirmed on Node.js 25.6.1 and requires WebAssembly exception handling and JSTag support to be enabled.
- Exploit availability: A proof-of-concept has been published (BleepingComputer).
- Technical mechanism (high level): BleepingComputer summarizes that WebAssembly exception handling can intercept JavaScript errors at a lower level in V8, bypassing vm2’s JavaScript-based defenses. A crafted error path (involving a Symbol-to-string conversion) can cause a host-side error object to leak back into the sandbox without proper sanitization.
- Still unclear
- Scope across versions: BleepingComputer notes earlier vm2 releases may also be vulnerable, but this is not confirmed.
- Broader Node.js impact: The advisory reportedly limits impact to Node.js 25 with specific features enabled. It is not stated whether other Node.js versions or default configurations are affected.
Practical next steps
If your applications execute user-supplied JavaScript with vm2, focus on the following actions that are supported by the current evidence:
- Upgrade vm2 to at least version 3.10.5, which NVD states contains the patch.
- Verify whether your runtime matches the reported preconditions: Node.js 25 (confirmed on 25.6.1) with WebAssembly exception handling and JSTag enabled. If it does, prioritize the update.
- Review the project’s advisory and recent release notes to confirm applicability in your environment. BleepingComputer links to the maintainer’s advisory and release tags for additional details.
A measured view of risk
The combination of a sandbox escape, confirmed impact on a current Node.js branch, and publicly available PoC raises the likelihood of real-world testing by attackers. At the same time, the reported preconditions narrow exposure to specific Node.js 25 configurations. Teams not running Node.js 25 with those features enabled may be outside the demonstrated impact, but updating vm2 remains the most straightforward way to reduce uncertainty.
References
- NVD entry (via vm2 3.10.5 release notes): https://github.com/patriksimek/vm2/releases/tag/v3.10.5
- BleepingComputer coverage: https://www.bleepingcomputer.com/news/security/critical-vm2-sandbox-bug-lets-attackers-execute-code-on-hosts/
—
Author: Alex Mira, AI Research Writer at Toolslib
Disclosure: This article summarizes information from public sources and project materials linked above. Claims are limited to what those sources report at the time of writing.
Alex Mira is a fictitious AI-assisted author created for the Toolslib blog. Designed to support cybersecurity education, Alex writes about malware trends, software utilities, privacy practices, Windows internals, and practical defensive workflows. Articles published under Alex’s name are generated or assisted by AI and reviewed according to Toolslib’s editorial standards before publication.
Stay Updated with ToolsLib! 🚀
Join our community to receive the latest cybersecurity tips, software updates, and exclusive insights straight to your inbox!